IT Recycling for Healthcare: What NHS Trusts and Private Clinics Must Do Differently
“IT recycling for healthcare is the process of securely disposing of clinical and administrative IT equipment — including computers, medical devices with embedded storage, and mobile devices — in full compliance with UK GDPR, the Data Security and Protection Toolkit, NHS data security standards, and WEEE regulations. Healthcare organisations require certified data destruction with per-device documentation because of the highly sensitive nature of patient data held on clinical systems.”
Most data breaches are serious. A healthcare data breach is in a different category entirely.
When patient records are exposed — clinical histories, diagnoses, medications, mental health notes, HIV status, reproductive health decisions — the harm to the individuals affected goes far beyond inconvenience. People lose jobs. Insurance premiums increase. Relationships end. In cases involving mental health or stigmatised conditions, the impact can be devastating and permanent.
The ICO knows this. Healthcare data sits in a special category under UK GDPR — "special category data" — which attracts higher obligations and greater scrutiny than standard personal data. The ICO's enforcement record in the healthcare sector reflects this: healthcare organisations consistently appear in investigation reports for data incidents involving improper device disposal, and the penalties are proportionately severe.
I have spent time auditing IT asset management and disposal processes for businesses across Scotland, including organisations in regulated sectors. The gap I observe most consistently in healthcare settings is not a lack of awareness that data destruction matters. It is a misunderstanding of the standard required — and a tendency to use general business IT disposal processes in an environment where the obligations are fundamentally more demanding.
This post covers exactly what healthcare organisations need to do differently. What the specific regulatory framework looks like. What device categories require particular attention. What the data destruction standard needs to be. And what documentation a healthcare organisation should hold to demonstrate compliance if questions are ever asked.
Who This Is For
This is for you if:
You manage IT assets for an NHS trust, health board, GP practice, dental practice, private clinic, or care home in Scotland or the UK
You are responsible for information governance, data protection, or IT security in a healthcare setting
You are procuring IT disposal services and want to understand what the healthcare-specific requirements are
You have existing disposal processes and want to confirm they meet the standard required for clinical environments
This is not for you if:
You are a household individual disposing of personal medical devices
You are looking for guidance on clinical equipment disposal that does not involve data storage (medical waste has a separate regulatory framework)
The Regulatory Framework Healthcare Organisations Operate Under
Healthcare organisations in Scotland and across the UK face a layered compliance environment when disposing of IT equipment. Understanding each layer matters because the obligations do not simply stack — they interact, and failing one frequently means failing another.
UK GDPR and the Data Protection Act 2018
The baseline framework applies to all organisations. Patient data is special category data under Article 9 of UK GDPR, which means processing — including disposal — requires higher justification and more rigorous safeguards than standard personal data. The principle of integrity and confidentiality requires appropriate technical measures to prevent unauthorised access to patient data, including on devices being disposed of.
The Data Security and Protection Toolkit (DSPT)
NHS organisations in England, and organisations handling NHS patient data in any setting, are required to complete the Data Security and Protection Toolkit annually. The DSPT includes specific requirements around data destruction — organisations must demonstrate that personal data is securely destroyed when no longer needed, and that this is documented.
Scotland operates under a similar framework through NHS Scotland's Digital Information Security Policy, which aligns with the DSPT principles and carries equivalent expectations around secure data disposal.
NHS Digital (now NHS England) Data Security Standards
The ten National Data Guardian standards for data security include explicit requirements around the removal of access to data when it is no longer needed. Standard 7 specifically addresses continuity and covers the proper handling of data during decommissioning of IT systems and devices.
WEEE Regulations
The Waste Electrical and Electronic Equipment regulations apply to healthcare organisations in exactly the same way they apply to all businesses. Electronic equipment — including clinical devices with embedded storage — must be disposed of through authorised channels with appropriate documentation.
Caldicott Principles
While the Caldicott Principles primarily govern the use and sharing of patient information, the seventh principle — "The duty to share information can be as important as the duty to protect patient confidentiality" — and the broader framework of Caldicott governance reinforce the obligation to treat patient data with exceptional care at every stage of its lifecycle, including at disposal.
📌 Related read: IT Recycling and GDPR Compliance in Scotland — the broader GDPR compliance framework for IT disposal, including what documentation healthcare organisations need to hold.
The Device Categories That Create the Most Risk in Healthcare
Healthcare environments contain a broader range of data-bearing devices than most business settings. Each category carries specific risks that a general IT disposal process may not adequately address.
Clinical Workstations and Laptops
These are the most obvious category. Clinical workstations — desktop computers and laptops used at nursing stations, in consultation rooms, and in administrative offices — hold or have held access to patient record systems. Even if the device connects to a centralised system rather than storing data locally, cached credentials, browser histories, locally saved documents, and temporary files can remain on the device's storage.
The data destruction requirement here is identical to any business device: certified erasure to a recognised standard, with a per-device certificate identifying the serial number and the method used. The difference in a healthcare context is the consequence of failure — patient clinical records are special category data, and their exposure carries significantly higher regulatory and reputational consequences.
Medical Devices with Embedded Storage
This is the category most often missed entirely in healthcare IT disposal processes. Modern medical equipment — diagnostic imaging machines, ECG monitors, infusion pumps, patient monitoring systems, and even some physiotherapy equipment — frequently contains embedded computers running standard operating systems on standard storage media.
These devices process, store, and in some cases transmit patient data. When a piece of medical equipment is decommissioned, the data on its embedded storage is subject to exactly the same GDPR obligations as data on a clinical workstation. But the disposal pathway for medical equipment is often handled separately from IT equipment — through biomedical engineering or facilities management rather than the IT department — and data destruction is not always part of that process.
I have seen organisations correctly process their clinical workstations through certified data destruction while simultaneously handing old diagnostic equipment to a medical device reseller without any data erasure. The workstations were documented. The diagnostic machines were not. Both held patient data.
Mobile Devices
NHS organisations and private healthcare providers use mobile devices extensively — smartphones for clinical communications, tablets for patient data entry at the bedside, and personal devices enrolled in bring-your-own-device programmes. Each of these may hold: patient identifiers, clinical photographs, secure messaging content, and authentication credentials for clinical systems.
Mobile device data destruction requires specialist software — the same reasons that make standard overwrite ineffective on SSDs apply to the NAND flash storage in smartphones and tablets. Certified mobile erasure software, or physical destruction, is required.
📌 Related read: How IT Recycling Works Step by Step — including the full processing chain that certified equipment goes through from collection to certification.
Servers and Network Equipment
NHS trusts and large private healthcare providers operate significant server infrastructure — patient administration systems, picture archiving and communication systems (PACS), electronic patient records, and clinical decision support systems all run on server infrastructure that holds enormous volumes of patient data.
Decommissioning a server in a healthcare environment requires the most rigorous approach available. Per-device data destruction certificates identifying every storage device by serial number. Chain-of-custody documentation from the point the device is powered off to the point of certified destruction. For servers holding imaging data or other particularly sensitive records, on-site destruction — where the drives are destroyed before the equipment leaves the premises — is frequently the appropriate standard.
Network equipment in healthcare environments may hold configuration data, VPN credentials, and access logs that could expose network architecture and, indirectly, pathways to clinical systems. This equipment requires data handling as part of its disposal, not just WEEE compliance.
Photocopiers and Multifunction Devices
Healthcare settings use photocopiers and multifunction devices extensively — for patient letters, referral documents, prescription forms, and administrative correspondence. Modern multifunction devices store copies of every document processed. In a clinical setting, that means the device's hard drive may contain thousands of patient documents — letters, test results, referral forms — accumulated over years of operation.
This is a consistent blind spot. I have reviewed disposal processes for healthcare organisations where clinical workstations were processed with rigorous data destruction and the photocopiers in the same office were simply returned to the leasing company at end of contract — without any data destruction whatsoever. The leasing company was not a certified data destruction provider. The devices went back into the market.
Every photocopier and multifunction device leaving a healthcare environment must have its internal storage erased or physically destroyed before it leaves the premises.
The H-C-D Framework: Healthcare-Specific Data Destruction Standards
Based on the specific obligations healthcare organisations face, I use a framework I call the H-C-D System to guide disposal decisions in clinical environments. It addresses the three dimensions where healthcare disposal requirements exceed standard business requirements.
H — Higher Assurance Standard
The data destruction method used in healthcare settings should default to a higher assurance standard than standard business disposal. For HDDs, certified multi-pass overwrite to a recognised standard remains appropriate, but physical destruction should be the default for any drive where verification is uncertain. For SSDs, physical destruction is the recommended default — not ATA Secure Erase with a physical destruction fallback, but physical destruction as the primary method — given the volume and sensitivity of patient data involved.
For mobile devices and embedded clinical equipment storage, on-site destruction or certified mobile erasure with physical destruction as the fallback is the appropriate standard.
The reason for defaulting to physical destruction more readily than a standard business would is simple: the harm from a failed erasure in a healthcare environment — patient clinical records exposed — is categorically more serious than the harm from a failed erasure in most other environments.
C — Chain of Custody Documentation
Healthcare organisations need a more detailed chain-of-custody record than standard businesses typically request. This means: a documented inventory of every data-bearing device before collection, a signed handover record at the point of collection identifying devices by serial number, confirmation of secure transport (locked vehicle, tracked, insured), and a receiving confirmation from the processing facility.
The chain-of-custody record closes the gap between a device leaving the organisation and the data destruction certificate being issued. Without it, there is a period — potentially hours or days — during which the location and security status of devices containing patient data is unconfirmed. In a healthcare environment, that gap is a compliance exposure.
D — Detailed Per-Device Certificates
Healthcare organisations must hold per-device data destruction certificates identifying every data-bearing device — not just laptops and workstations, but servers, mobile devices, embedded clinical equipment storage, and photocopier hard drives. Each certificate must include: the device serial number, the destruction method used, the standard applied, the date of processing, and verification status.
These certificates are the primary evidence of compliance in an ICO investigation or a DSPT audit. Batch certificates covering quantities without serial numbers, certificates that do not specify the method used, or certificates that do not cover all device categories — all of these leave documentation gaps that weaken the compliance position.
📌 Related read: IT Recycling for Scotland Businesses — how organisations across Scotland are structuring compliant disposal processes, including in regulated sectors.
What an ICO Investigation into Healthcare IT Disposal Actually Looks At
Healthcare organisations that have faced ICO investigations following data incidents involving device disposal report that investigators focus on a consistent set of questions. Understanding these in advance shapes what documentation you need to hold and what processes you need to have in place.
Did the organisation have a documented IT disposal policy? A written policy covering how devices are assessed, who is authorised to arrange disposal, what data destruction standard is required, what documentation must be obtained, and how certificates are stored and retained. The absence of a policy is itself evidence of inadequate organisational measures.
Was the provider certified and authorised? Investigators will ask for evidence that the provider was a licensed waste carrier and an AATF. Using an unlicensed provider — even inadvertently — significantly worsens the compliance position.
Can the organisation produce a certificate for the specific device in question? This is the moment when the difference between a batch certificate and a per-device certificate becomes critical. If a specific device is identified as potentially involved in a data incident, the organisation needs to be able to produce a certificate that identifies that specific device by serial number and confirms the destruction method and date.
Were all device categories covered? Investigators do not just look at workstations. If medical devices, photocopiers, or mobile devices were not included in the data destruction process, that gap will be identified.
Building an IT Disposal Policy for Healthcare
Every healthcare organisation — from a single GP practice to a large NHS trust — needs a written IT disposal policy. This is not a bureaucratic exercise. It is the organisational measure that demonstrates, in any investigation, that the organisation took its obligations seriously and had a process in place.
A healthcare IT disposal policy should cover:
Scope. Every category of device the policy applies to — clinical workstations, laptops, servers, mobile devices, medical equipment with embedded storage, photocopiers and MFDs, removable media.
Responsibility. Who is authorised to arrange disposal. Who is responsible for obtaining and storing certificates. Who reviews the process.
Data destruction standard. The minimum standard required for each device category. For healthcare, this should specify physical destruction as the default for SSDs and mobile devices.
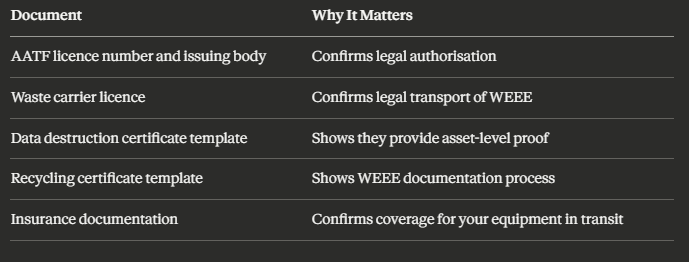
Provider requirements. The minimum credentials a disposal provider must hold — licensed waste carrier, AATF status, ability to produce per-device certificates, chain-of-custody documentation.
Documentation retention. How long certificates are kept (minimum three years; longer for clinical environments given the potential duration of regulatory investigations) and where they are stored.
Review cycle. How often the policy is reviewed — at minimum annually, and whenever the DSPT is completed.
📌 Related read: Small Business IT Recycling Guide — a practical starting point for smaller healthcare organisations such as GP practices and dental clinics building their first disposal policy.
Selecting a Certified Provider for Healthcare IT Disposal
The provider selection process for healthcare IT disposal requires greater scrutiny than for standard business disposal. The additional questions to ask — beyond the baseline licence and certificate questions — include:
Do you have experience in healthcare or clinical environments? Experience matters because healthcare disposal involves device categories and sensitivity levels that general IT recyclers may not have encountered. A provider with healthcare clients should be able to describe specific adaptations to their process for clinical environments.
Can you provide on-site data destruction? For high-sensitivity decommissioning — server rooms, clinical workstations holding long-term patient records, or medical devices with embedded patient data — on-site destruction may be the appropriate standard. Ask whether the provider offers this and what the process looks like.
How do you handle medical devices with embedded storage? This question separates providers who understand healthcare disposal from those who are treating all devices as standard IT equipment. A prepared provider will describe a process for assessing embedded storage in clinical devices and applying appropriate destruction methods.
What is your chain-of-custody process? For healthcare, ask specifically for a written description of how devices are secured from point of collection to processing — vehicle type, tracking, access controls at the facility, and the point at which the chain-of-custody record is complete.
Can you support DSPT evidence requirements? A provider familiar with NHS procurement will understand the DSPT and be able to produce documentation in formats that support the annual submission.
📌 Related read: IT Recycling vs IT Disposal in Scotland — why the choice of provider and disposal route matters as much as the decision to dispose of equipment at all.
Key Takeaways
Patient data is special category data under UK GDPR — healthcare IT disposal obligations are categorically more demanding than standard business disposal
The regulatory framework for healthcare includes UK GDPR, the Data Security and Protection Toolkit, NHS Digital data security standards, and WEEE regulations — all simultaneously
The device categories most often mishandled in healthcare are medical devices with embedded storage, photocopiers and multifunction devices, and mobile devices enrolled in clinical programmes
The H-C-D Framework covers the three dimensions of healthcare-specific disposal: Higher assurance standard, Chain-of-custody documentation, and Detailed per-device certificates
Physical destruction should be the default — not the fallback — for SSDs, mobile devices, and embedded clinical equipment storage in healthcare environments
Chain-of-custody documentation that covers the period between collection and processing is a healthcare-specific requirement that standard businesses rarely obtain
Every healthcare organisation needs a written IT disposal policy covering all device categories, provider requirements, and documentation retention
An ICO investigation will ask for a certificate identifying a specific device by serial number — batch certificates without serial numbers do not provide adequate compliance protection
Provider selection for healthcare requires additional scrutiny: experience with clinical environments, on-site destruction capability, and familiarity with DSPT evidence requirements
The DSPT annual submission should be supported by disposal documentation — certificates and chain-of-custody records covering the period since the last submission
Frequently Asked Questions
1. Do GP practices and dental clinics have the same IT disposal obligations as NHS trusts? Yes. Any organisation handling NHS patient data or operating under NHS contracts is subject to the Data Security and Protection Toolkit requirements, including secure data disposal. Private clinics and dental practices handling patient records are subject to UK GDPR special category data obligations. The scale of the organisation does not change the standard — it affects the volume of documentation required, not the compliance threshold.
2. What should happen to a decommissioned diagnostic imaging machine? If the machine has embedded storage — which most modern diagnostic imaging equipment does — data destruction must be part of the decommissioning process before the equipment leaves the organisation's control. This should be coordinated between the IT or information governance team and the biomedical engineering or facilities team handling the physical decommissioning. A data destruction certificate identifying the storage device by serial number is required.
3. How should a healthcare organisation handle the disposal of a device that was reported stolen before it was recovered? If a device was reported as lost or stolen and subsequently recovered, it should be treated as a higher-risk item. The chain-of-custody gap — the period during which its location was unknown — should be documented. Data destruction should default to physical destruction rather than software erasure, and the destruction certificate should be retained alongside the incident report in case the ICO investigates the original loss.
4. Can healthcare organisations donate refurbished IT equipment? Yes, but only after certified data destruction. Patient data must be irreversibly destroyed before any device leaves the organisation's control, regardless of where it is going. If a device is being donated to a charity, the data destruction certificate must precede the donation — not follow it. Some certified recyclers have established charity partnerships and can manage both the data destruction and the donation pathway within a single compliant process.
5. What evidence does the DSPT require for data destruction? The DSPT requires organisations to demonstrate that personal data is securely destroyed when no longer needed. In practice, this means holding data destruction certificates for devices disposed of during the relevant period, being able to describe the destruction standard used, and having a written disposal policy in place. Auditors may ask to review sample certificates and the policy document. Certificates without serial numbers or without specifying the destruction method are unlikely to satisfy DSPT evidence requirements.
If your healthcare organisation is disposing of IT equipment — whether routine end-of-life laptops, decommissioning clinical systems, or clearing a server room — the standard for data destruction and documentation in a clinical environment is higher than most general IT recyclers are prepared to meet.
Speaking to a certified provider with healthcare experience before you arrange a collection gives you the opportunity to confirm that the process, documentation, and chain-of-custody approach will meet your DSPT and GDPR obligations.